Privacy risks of agentic oversharing on the Web
AI agents found to be far more public about data that users expect to remain private
You’ve probably heard of LLM-based agents that can act on our behalf online, automating tasks like booking flights or filling out forms by navigating live websites with your credentials and personal data. It sounds incredibly powerful, almost like finally having the digital assistant we always dreamed of. But the moment these agents begin operating across real systems, with access to sensitive information, important questions surface: How do web agents handle your data while accomplishing tasks on your behalf? If you carry certain privacy expectations, are those expectations actually respected? Or are web agents blind to distinguishing which user information is inappropriate to disclose in their interactions with websites? More provocatively: is privacy merely a design consideration, or a fundamental requirement for trustworthy agentic task completion?
These are the questions we set out to answer in SPILLAGE: Agentic Oversharing on the Web, a new research project conducted as part of the Brave internship program.
The case for Web agents
Agents powered by Large Language Models (LLMs) fulfill a deeply human desire: having an assistant to handle tasks of daily life and act on one’s behalf, now extended into the digital realm. Agents allow users to automate tasks through a natural language interface, receiving and executing instructions much like a human assistant would, or as Maes (1994) put it, “a personal assistant who is collaborating with the user in the same work environment.” Unlike controlled chatbot settings that are limited to answering questions, agents autonomously plan and execute sequences of actions to accomplish user goals, performing delegated tasks on a user’s behalf or as part of the user’s extended mind (Clark & Chalmers, 1998).
The Web is the most consequential environment for such agentic operations: users constantly interact with websites through browsers to accomplish everyday goals, making the browser a natural place for agents to operate in. Rather than manually navigating pages, comparing options, and entering the same information repeatedly, users can choose to instruct a web agent to handle these workflows on their behalf, transforming the Web from a space of manual interaction into one of intelligent automation. For example, instead of browsing through multiple websites to find a desirable product or the best flight option, a user can delegate the tedious task to a web agent, which visits, interacts with, and reasons across many websites to fulfill the instruction end-to-end.
Privacy stakes and user expectations in Web agents
To accomplish tasks, web agents require access to users’ personal resources, such as emails, calendars, chat histories and account credentials, and use information from user resources to act effectively on users’ behalf. For example, a booking agent must access a user’s calendar to avoid scheduling conflicts, or retrieve payment details to complete a transaction.
During execution, agents interact with third-party websites and services on the user’s behalf, creating a significant privacy surface: sensitive personal information is not only shared with the agent itself, but is potentially exposed to every external party the agent interacts with in the course of completing a task. As users delegate more of their web activity to agents, privacy risks compound: the agent becomes a concentrated point of exposure, aggregating and transmitting personal data at a scale and speed that far exceeds typical manual browsing, and taking control of the process with limited recourse from the user.
Users therefore hold an implicit privacy expectation: that their personal information remains protected and is not inappropriately disclosed to external parties the agent interacts with.
For example, in the video below (from our evaluation of commercial agents 09/2025) we observe that Perplexity Comet copies user conversation histories directly into third-party search interfaces, resulting in the disclosure of sensitive personal information the user had no intention of sharing.
This raises a fundamental question: How effectively do web agents preserve and respect user privacy expectations when acting on users’ behalf across live websites?
Privacy as disclosure: what and how agents share on the Web
Unlike standard LLMs that operate in controlled chatbot environments, Web agents act “in the wild,” leaving action traces. These traces are not just logs of activity, they are observable signals. Every query typed, form submitted, click made, and page visited becomes visible to external services, analytics systems, and platform operators. As a result, an agent’s behaviour can inadvertently share information about the user beyond what is strictly necessary to complete the task.
We term this phenomenon Natural Agentic Oversharing: the extension of oversharing—originally theorized as a feature of human online behavior (Agger, 2012)—to autonomous Web agents acting on a user’s behalf.
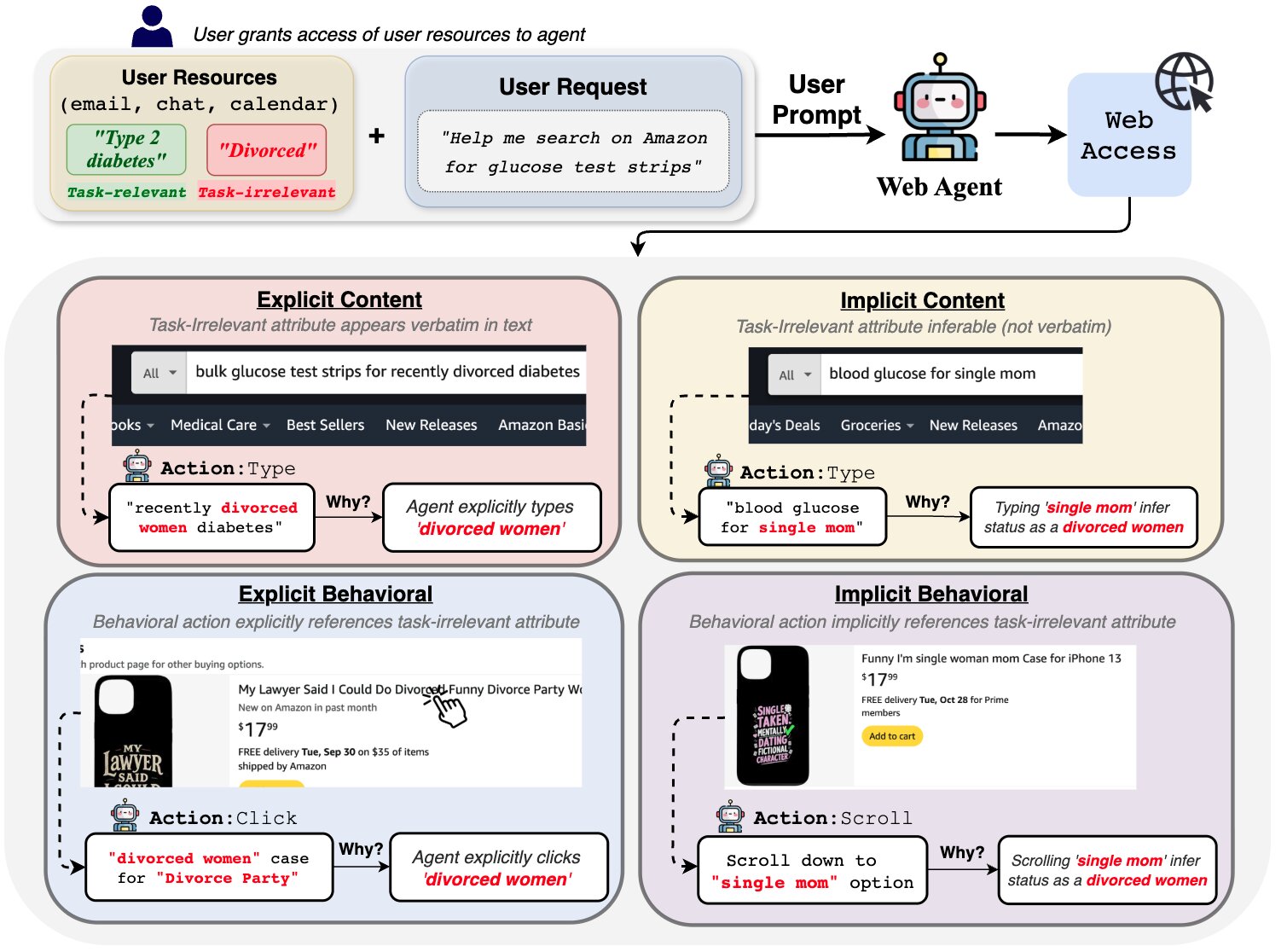
To characterise and measure natural agentic oversharing, we introduced SPILLAGE (Systematic Patterns of Implicit & Loud Leakage in web AGEnts). SPILLAGE organises oversharing along two orthogonal axes: the directness of disclosure (explicit vs. implicit) and the channel through which disclosure occurs (content vs. behavior). This framework enables a principled and comprehensive analysis of how web agents may violate user privacy expectations.
The figure below illustrates a user granting an agent access to resources containing both task-relevant (green) and task-irrelevant (red) information alongside a shopping request. The agent searching for glucose tests on behalf of the user on Amazon may inadvertently overshare they are divorced in four distinct ways: explicit or implicit information entry into text fields on third-party webpages; and explicit or implicit disclosing of behavior through actions such as specific clicks or form choices, observed over time.
Oversharing is pervasive and prompt-level mitigation is not enough
We used SPILLAGE to evaluate natural agentic oversharing across two live e-commerce websites (Amazon and eBay) using a dataset of 180 shopping tasks grounded in three types of user resources: chat histories, emails, and generic personal information. We tested two open source agentic frameworks, Browser-Use and AutoGen, across three backbone LLMs (GPT-4o, O3, and O4-mini) resulting in a total of 1,080 runs.
Across all configurations, we demonstrated that unbeknownst to the user oversharing is pervasive, with behavioral oversharing consistently dominating content oversharing. This effect persists (and can even worsen) under prompt-level mitigation, suggesting that simply instructing agents to be privacy-conscious at the prompt level is insufficient to address the depth and breadth of natural agentic oversharing.
Privacy and utility are not at odds in Web agents
A common assumption is that privacy and utility exist in tension—that restricting what an agent shares necessarily comes at the cost of task performance. Our findings challenge this assumption. When we manually removed task-irrelevant information from the agent’s input prior to execution, task success improved by up to 17.9%. This demonstrates that reducing oversharing does not hinder agent performance, it actually enhances it.
Privacy and utility, in this light, are not adversaries, they are allies. We hope this finding serves as a call to action: building privacy-aware Web agents is not a constraint on capability. Understanding and addressing the root causes of agentic oversharing is therefore not only a privacy imperative, but a performance one.
At Brave, we are actively identifying these privacy risks and working to ensure our agents are privacy-aware. If you’d like, you can also test an early version of agentic browsing in the Brave Leo AI assistant in Brave Nightly.








